How to Secure Your Cryptocurrency in 2026
How to Secure Your Cryptocurrency in 2026

How to Secure Your Cryptocurrency in 2026
How to Secure Your Cryptocurrency in 2026

TL;DR: Cryptocurrency theft reached $3.4 billion in 2025, but most losses come from user error and protocol vulnerabilities rather than technical breaches. Secure your crypto using hardware wallets for long-term storage, enable two-factor authentication everywhere, research audits before using DeFi protocols, and adopt daily security habits like avoiding public WiFi and verifying addresses carefully. The difference between a secured portfolio and a compromised one often comes down to discipline and asking the right questions before you deposit.
Key takeaways
Hardware wallets like Trezor Safe 7 and Ledger Flex remain the gold standard for long-term crypto storage, with institutions now adopting cold storage at a 74% rate
DeFi protocols require extra scrutiny beyond exchange accounts, including audit verification from firms like CertiK, OpenZeppelin, or Quantstamp before depositing significant funds
AI-enabled scams increased 450% year-over-year in 2025, making verification habits (checking URLs, confirming addresses, using hardware wallet confirmations) non-negotiable
Two-factor authentication adoption jumped from 47% to 82% in 2025, reducing account compromises by 59%, making it the single most impactful security step most people skip
You probably didn't lose sleep over your bank account security in 2025. Banks have insurance, fraud departments, and decades of institutional safeguards. Your crypto portfolio doesn't. When you hold digital assets, you become the bank. That responsibility is both liberating and terrifying. The good news: securing your crypto in 2026 is simpler and more accessible than ever. The challenge is that simplicity doesn't mean autopilot.
This guide covers what actually matters for keeping your cryptocurrency safe, stripped of the hype and the "trust me bro" advice you'll find everywhere else.
The threat picture in 2026
Let's start with reality. In 2025, crypto theft reached $3.4 billion in direct transfers. When you include fraud, exit scams, and other losses, the total hit $17 billion, according to the Chainalysis 2026 Crypto Crime Report. The Bybit hack in February 2025 alone cost users $1.5 billion, making it the largest cryptocurrency theft ever recorded.
But here's what matters more than the numbers: most of these losses were preventable. North Korean hackers stole $2.02 billion in 2025, but they targeted exchanges and institutional wallets, not individuals with hardware wallets and decent password hygiene. The fastest-growing threat isn't technical. It's social. AI-enabled scams jumped 450% year-over-year in 2025. Impersonation attacks surged 1,400%. These aren't exploits. They're deception.
The pattern is clear. If you control your own keys and don't fall for fake messages, your cryptocurrency is significantly safer than most people assume. If you skip the basics, you're exposed.
Hardware wallets and cold storage
Hardware wallets are physical devices that store your private keys offline. They remain the industry standard for serious crypto holders. When you use a hardware wallet, you sign transactions on the device itself. Your keys never touch your computer or phone. This single design choice eliminates most attack vectors.
The current generation of hardware wallets is far better than older models. Trezor Safe 7 and Ledger Flex both offer better usability and security features than their predecessors. Older models like Trezor Safe 3 still work well and cost less if you're budget-conscious. The key difference isn't the brand. It's that your keys stay in a device you control, not on an exchange server.
Institutions get this. 74% of institutional investors now use cold storage for their cryptocurrency holdings. They're not being paranoid. They're being professional. If you're holding crypto long-term, especially if you own significant amounts, a hardware wallet is mandatory, not optional.
Storage matters too. Keep your hardware wallet somewhere secure but accessible. A safe or a safety deposit box works. Don't leave it on your desk next to your laptop. If your home is compromised, physical security becomes relevant. More importantly, write down your recovery seed (the 12 or 24 word phrase that restores your wallet if the device breaks). Store this seed separately from the device, somewhere fireproof if possible. Never store your seed digitally. Never take a screenshot. Never store it in a password manager, a notes app, or a cloud backup. Write it on paper. This feels low-tech, but it's the most secure approach available.
Why DeFi requires different rules than exchange accounts
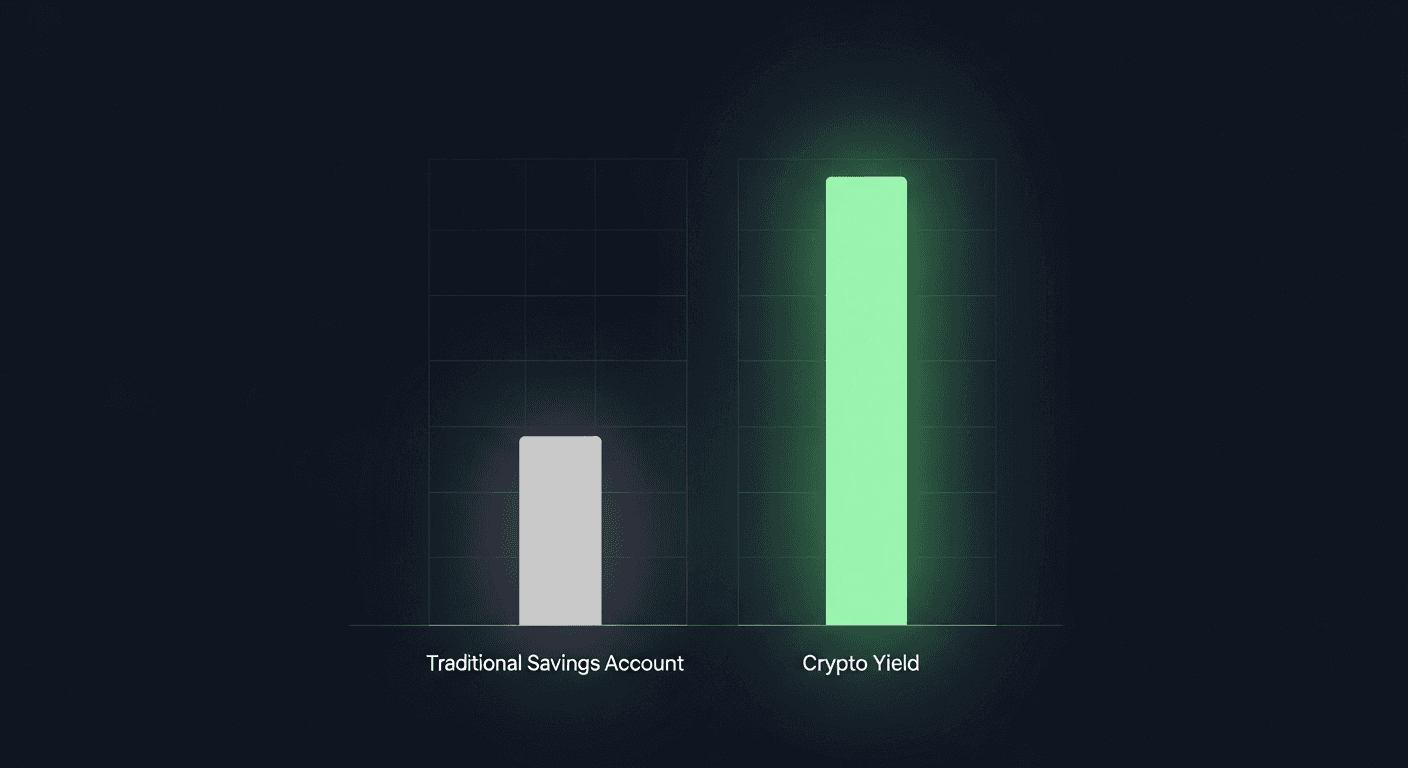
Decentralized finance runs on smart contracts, which are programs stored on the blockchain. Unlike centralized exchanges, DeFi platforms don't hold your assets in a corporate wallet. You deposit your crypto into a smart contract, and that contract decides how to use your funds. This gives you more control and better returns. It also means the protocol itself can fail.
Exchange accounts are custodial. If an exchange gets hacked, the company is liable. Most major exchanges now carry insurance. DeFi is non-custodial. If a smart contract has a vulnerability and it gets exploited, your money can vanish. No insurance. No customer service line. No CEO to sue. This isn't scaremongering. Between 2020 and 2025, DeFi vulnerabilities cost users $4.2 billion despite the fact that many protocols are audited.
This doesn't mean DeFi is dangerous. It means DeFi requires homework. You need to understand what you're depositing into, whether the protocol has been tested by real security experts, and how much risk you're taking with each vault or strategy.
The audit question: how to know if a protocol is safe
An audit is a security assessment. A team of engineers reviews the smart contract code line by line, looking for bugs, vulnerabilities, and logical flaws. Good audits catch most problems. Not all problems. No audit guarantees safety.
The audit firms that matter include CertiK (which has conducted over 5,500 audits), OpenZeppelin, Quantstamp, and Trail of Bits. These are not the only reputable auditors, but they're the ones with proven track records and transparent reporting. If you're considering a DeFi protocol, check whether it's been audited by one of these firms or another well-respected one. Read the audit report, not just the summary. Audit reports flag issues and whether they were fixed.
Top protocols like Aave, Compound III, and Morpho have undergone multiple audits. This doesn't mean they're immune to problems. It means they've had expert eyes on their code and they've fixed what those experts found. There's a difference between "audited" and "safe forever." Audits are snapshots in time. If a protocol adds new features, it should get new audits. If you see a protocol claiming one audit from years ago and nothing since, treat it as a red flag.
Also check DefiLlama's hacks tracker, which catalogs historical exploits. If a protocol got hacked, what was the vulnerability, and how did they fix it? If it got hacked twice, why? If the team didn't fix the underlying issue, run.
Questions to ask before depositing funds anywhere
You've heard of the protocol. Maybe your friends use it. Maybe the yield looks amazing. Before you send your crypto, ask these questions.
Who runs this protocol, and can they disappear? Truly decentralized protocols are run by DAOs (Decentralized Autonomous Organizations) with distributed governance. Semi-decentralized protocols are still controlled by a team. Anonymous teams are higher risk. If the team can unilaterally change the rules or extract funds, you're trusting people, not code. Know what you're trusting.
What's the audit history? Ask directly. If the protocol can't point you to a recent, reputable audit, be skeptical. New protocols should have at least one audit before they handle significant user funds. Established protocols should have multiple audits over time.
What happens if something breaks? Does the protocol have an insurance fund? Can you pause withdrawals? If there's an exploit, how long does it take to fix? Can users exit? Protocols with emergency pause mechanisms and user-controlled exit options are safer than rigid ones.
What's the yield based on? Unsustainably high yields come from one place: capital. If a protocol promises 40% APY, someone is paying that. If it's not coming from protocol revenue or incentives, it's likely coming from user capital. That's a Ponzi. Real yields (like Aave lending rates) fluctuate based on supply and demand. Impossible yields are the first warning sign.
This is where many people make their first real security investment. Platforms like Pistachio.fi exist because most DeFi platforms don't do this homework for you. Pistachio curates vaults and rates each one on a 1-10 risk scale. You get audit verification, smart contract security grading, and real institutional-grade oversight. It removes the need to audit protocols yourself, which most retail users aren't equipped to do anyway. The point is simple: if a platform isn't willing to tell you why a vault is safe, don't use it.
Practical daily habits that most guides skip
Hardware wallets and audits are the foundation. Daily habits are the roof that actually stops the rain.
Verify addresses every single time. Copy-paste the address you're sending to from official sources. Don't trust it from a tweet, a Discord message, or an email. When you paste the address into your wallet, does the first part and last few characters match? Your hardware wallet screen will show you the full address when you confirm the transaction. Check it. Malware that replaces copied addresses with attacker addresses exists and spreads. This takes 10 seconds and it stops most phishing.
Use two-factor authentication everywhere. In 2025, 82% of crypto users enabled 2FA, and those users saw 59% fewer account compromises. That's the single biggest improvement you can make today. Use an authenticator app (Google Authenticator, Authy, Bitwarden), not SMS. SMS can be hijacked. Apps can't. If a platform offers hardware key support (Yubikey, for example), use that instead. It's overkill for most people, but it's the strongest option available.
Never use public WiFi for crypto transactions. Public WiFi is trivial to intercept. Your password, your seed phrase, your transaction confirmations, your private keys: all of it can be captured. This isn't theoretical. Do your crypto work on your home network or your mobile hotspot. That's it.
Assume every message claiming to be from a platform is fake until you verify it. Phishing emails, Discord DMs, Twitter replies: they're all designed to make you click a malicious link or enter your seed phrase. Legitimate platforms never ask for your seed phrase. Ever. If you got a message asking for it, report and block the sender. If you're unsure, go directly to the official website by typing the URL yourself. Don't click links in messages.
Keep your software updated. Your phone's operating system, your wallet software, your browser, your antivirus. Updates patch vulnerabilities. Staying on old versions is like leaving your front door unlocked while you advertise that nobody's home. This sounds basic because it is, but it's often skipped.
Consider using a separate device for crypto if you hold significant amounts. A dedicated phone or laptop that only handles wallet operations, signing transactions, and nothing else eliminates most malware vectors. This is extreme for most people. If you're holding $100,000 or more, it becomes reasonable.
What the OWASP Smart Contract Top 10 2026 tells us
In early 2026, the Open Web Application Security Project (OWASP) published the Smart Contract Top 10, ranking the most common smart contract vulnerabilities. The list includes reentrancy attacks (where a smart contract function calls another function that calls it back before the first execution completes), access control failures, and arithmetic issues. These aren't new problems. They're the problems that auditors look for.
Why mention this? Because when you see an audit from a firm that checks the OWASP Top 10 against the code, you know they're using a proven framework. It's not a guarantee, but it's a signal of professional work.
Your crypto holdings and insurance questions
One more thing: if you're holding crypto on an exchange for active trading, check whether that exchange has insurance. Major exchanges like Kraken and Coinbase offer some coverage. The limits are usually lower than you'd like, but it's better than zero. This is one reason to keep long-term holdings on a hardware wallet and active trading capital on an exchange. Different tools for different jobs.
FAQ
What's the safest way to store cryptocurrency?
Hardware wallets held in your personal possession, with your recovery seed written on paper and stored separately. This is non-custodial storage. You control the keys. Nobody can freeze your account, change the rules, or take your money without your permission. For amounts you hold long-term and don't trade frequently, this is the standard.
Are hardware wallets really necessary if I use a reputable exchange?
It depends on your holdings and risk tolerance. For small amounts you're actively trading, an exchange with insurance and strong security is fine. For amounts you're holding long-term, especially more than a few thousand dollars, a hardware wallet removes counterparty risk. The Bybit hack in 2025 hit users of a supposedly reputable exchange. Hardware wallets protect you from that scenario entirely.
How do I know if a DeFi protocol is safe to use?
Look for a recent audit from a recognized firm (CertiK, OpenZeppelin, Quantstamp, Trail of Bits). Read what the audit found and whether it was fixed. Check the protocol's history on DefiLlama's hacks tracker. Understand where the yield comes from. If the protocol is new and unaudited but offering massive returns, it's probably a scam. If it's been audited and used by other projects you trust, it's lower risk. No audit means no deposit of significant funds.
What should I do immediately if I think my wallet has been compromised?
First, don't panic. Move any remaining funds to a new wallet on a different device. Generate a new hardware wallet if you can. Check your transaction history to see what was stolen and when. If you were using an exchange account that's compromised, change the password and enable 2FA if you haven't already. Consider whether your email or other accounts were also breached (check haveibeenpwned.com). If you suspect a smart contract exploit rather than a personal hack, notify the protocol team immediately through official channels. Most exploits can't be reversed, but the team needs to know to fix the vulnerability.
Does using a VPN protect my crypto?
A VPN masks your IP address but doesn't protect your private keys or stop you from clicking malicious links. If you're worried about ISP surveillance or network-level attacks on public WiFi, a VPN helps. If you're worried about hacking, a VPN alone won't save you. Use a VPN for privacy. Use a hardware wallet and good habits for security. They're different problems with different solutions.
Securing your cryptocurrency in 2026 doesn't require becoming a security engineer. It requires discipline. Use a hardware wallet for long-term holdings. Enable 2FA. Check audit history before using DeFi. Verify every address before you send funds. Don't use public WiFi. Don't trust messages claiming to be from official sources until you verify them directly. These habits sound repetitive because they work. The crypto users who lose funds are almost never the ones following this checklist. They're the ones skipping it and assuming someone else did the work for them.
If DeFi is part of your strategy, go beyond basic security. Use platforms like Pistachio.fi that do the audit verification and protocol vetting for you. The yield isn't worth the risk if the protocol is compromised. Read through Pistachio's security overview or compare options on their best crypto yield platforms guide. The work upfront saves you from panic later.
Your cryptocurrency is as secure as your habits allow it to be. Make the habits good.
Published: March 3, 2026
TL;DR: Cryptocurrency theft reached $3.4 billion in 2025, but most losses come from user error and protocol vulnerabilities rather than technical breaches. Secure your crypto using hardware wallets for long-term storage, enable two-factor authentication everywhere, research audits before using DeFi protocols, and adopt daily security habits like avoiding public WiFi and verifying addresses carefully. The difference between a secured portfolio and a compromised one often comes down to discipline and asking the right questions before you deposit.
Key takeaways
Hardware wallets like Trezor Safe 7 and Ledger Flex remain the gold standard for long-term crypto storage, with institutions now adopting cold storage at a 74% rate
DeFi protocols require extra scrutiny beyond exchange accounts, including audit verification from firms like CertiK, OpenZeppelin, or Quantstamp before depositing significant funds
AI-enabled scams increased 450% year-over-year in 2025, making verification habits (checking URLs, confirming addresses, using hardware wallet confirmations) non-negotiable
Two-factor authentication adoption jumped from 47% to 82% in 2025, reducing account compromises by 59%, making it the single most impactful security step most people skip
You probably didn't lose sleep over your bank account security in 2025. Banks have insurance, fraud departments, and decades of institutional safeguards. Your crypto portfolio doesn't. When you hold digital assets, you become the bank. That responsibility is both liberating and terrifying. The good news: securing your crypto in 2026 is simpler and more accessible than ever. The challenge is that simplicity doesn't mean autopilot.
This guide covers what actually matters for keeping your cryptocurrency safe, stripped of the hype and the "trust me bro" advice you'll find everywhere else.
The threat picture in 2026
Let's start with reality. In 2025, crypto theft reached $3.4 billion in direct transfers. When you include fraud, exit scams, and other losses, the total hit $17 billion, according to the Chainalysis 2026 Crypto Crime Report. The Bybit hack in February 2025 alone cost users $1.5 billion, making it the largest cryptocurrency theft ever recorded.
But here's what matters more than the numbers: most of these losses were preventable. North Korean hackers stole $2.02 billion in 2025, but they targeted exchanges and institutional wallets, not individuals with hardware wallets and decent password hygiene. The fastest-growing threat isn't technical. It's social. AI-enabled scams jumped 450% year-over-year in 2025. Impersonation attacks surged 1,400%. These aren't exploits. They're deception.
The pattern is clear. If you control your own keys and don't fall for fake messages, your cryptocurrency is significantly safer than most people assume. If you skip the basics, you're exposed.
Hardware wallets and cold storage
Hardware wallets are physical devices that store your private keys offline. They remain the industry standard for serious crypto holders. When you use a hardware wallet, you sign transactions on the device itself. Your keys never touch your computer or phone. This single design choice eliminates most attack vectors.
The current generation of hardware wallets is far better than older models. Trezor Safe 7 and Ledger Flex both offer better usability and security features than their predecessors. Older models like Trezor Safe 3 still work well and cost less if you're budget-conscious. The key difference isn't the brand. It's that your keys stay in a device you control, not on an exchange server.
Institutions get this. 74% of institutional investors now use cold storage for their cryptocurrency holdings. They're not being paranoid. They're being professional. If you're holding crypto long-term, especially if you own significant amounts, a hardware wallet is mandatory, not optional.
Storage matters too. Keep your hardware wallet somewhere secure but accessible. A safe or a safety deposit box works. Don't leave it on your desk next to your laptop. If your home is compromised, physical security becomes relevant. More importantly, write down your recovery seed (the 12 or 24 word phrase that restores your wallet if the device breaks). Store this seed separately from the device, somewhere fireproof if possible. Never store your seed digitally. Never take a screenshot. Never store it in a password manager, a notes app, or a cloud backup. Write it on paper. This feels low-tech, but it's the most secure approach available.
Why DeFi requires different rules than exchange accounts
Decentralized finance runs on smart contracts, which are programs stored on the blockchain. Unlike centralized exchanges, DeFi platforms don't hold your assets in a corporate wallet. You deposit your crypto into a smart contract, and that contract decides how to use your funds. This gives you more control and better returns. It also means the protocol itself can fail.
Exchange accounts are custodial. If an exchange gets hacked, the company is liable. Most major exchanges now carry insurance. DeFi is non-custodial. If a smart contract has a vulnerability and it gets exploited, your money can vanish. No insurance. No customer service line. No CEO to sue. This isn't scaremongering. Between 2020 and 2025, DeFi vulnerabilities cost users $4.2 billion despite the fact that many protocols are audited.
This doesn't mean DeFi is dangerous. It means DeFi requires homework. You need to understand what you're depositing into, whether the protocol has been tested by real security experts, and how much risk you're taking with each vault or strategy.
The audit question: how to know if a protocol is safe
An audit is a security assessment. A team of engineers reviews the smart contract code line by line, looking for bugs, vulnerabilities, and logical flaws. Good audits catch most problems. Not all problems. No audit guarantees safety.
The audit firms that matter include CertiK (which has conducted over 5,500 audits), OpenZeppelin, Quantstamp, and Trail of Bits. These are not the only reputable auditors, but they're the ones with proven track records and transparent reporting. If you're considering a DeFi protocol, check whether it's been audited by one of these firms or another well-respected one. Read the audit report, not just the summary. Audit reports flag issues and whether they were fixed.
Top protocols like Aave, Compound III, and Morpho have undergone multiple audits. This doesn't mean they're immune to problems. It means they've had expert eyes on their code and they've fixed what those experts found. There's a difference between "audited" and "safe forever." Audits are snapshots in time. If a protocol adds new features, it should get new audits. If you see a protocol claiming one audit from years ago and nothing since, treat it as a red flag.
Also check DefiLlama's hacks tracker, which catalogs historical exploits. If a protocol got hacked, what was the vulnerability, and how did they fix it? If it got hacked twice, why? If the team didn't fix the underlying issue, run.
Questions to ask before depositing funds anywhere
You've heard of the protocol. Maybe your friends use it. Maybe the yield looks amazing. Before you send your crypto, ask these questions.
Who runs this protocol, and can they disappear? Truly decentralized protocols are run by DAOs (Decentralized Autonomous Organizations) with distributed governance. Semi-decentralized protocols are still controlled by a team. Anonymous teams are higher risk. If the team can unilaterally change the rules or extract funds, you're trusting people, not code. Know what you're trusting.
What's the audit history? Ask directly. If the protocol can't point you to a recent, reputable audit, be skeptical. New protocols should have at least one audit before they handle significant user funds. Established protocols should have multiple audits over time.
What happens if something breaks? Does the protocol have an insurance fund? Can you pause withdrawals? If there's an exploit, how long does it take to fix? Can users exit? Protocols with emergency pause mechanisms and user-controlled exit options are safer than rigid ones.
What's the yield based on? Unsustainably high yields come from one place: capital. If a protocol promises 40% APY, someone is paying that. If it's not coming from protocol revenue or incentives, it's likely coming from user capital. That's a Ponzi. Real yields (like Aave lending rates) fluctuate based on supply and demand. Impossible yields are the first warning sign.
This is where many people make their first real security investment. Platforms like Pistachio.fi exist because most DeFi platforms don't do this homework for you. Pistachio curates vaults and rates each one on a 1-10 risk scale. You get audit verification, smart contract security grading, and real institutional-grade oversight. It removes the need to audit protocols yourself, which most retail users aren't equipped to do anyway. The point is simple: if a platform isn't willing to tell you why a vault is safe, don't use it.
Practical daily habits that most guides skip
Hardware wallets and audits are the foundation. Daily habits are the roof that actually stops the rain.
Verify addresses every single time. Copy-paste the address you're sending to from official sources. Don't trust it from a tweet, a Discord message, or an email. When you paste the address into your wallet, does the first part and last few characters match? Your hardware wallet screen will show you the full address when you confirm the transaction. Check it. Malware that replaces copied addresses with attacker addresses exists and spreads. This takes 10 seconds and it stops most phishing.
Use two-factor authentication everywhere. In 2025, 82% of crypto users enabled 2FA, and those users saw 59% fewer account compromises. That's the single biggest improvement you can make today. Use an authenticator app (Google Authenticator, Authy, Bitwarden), not SMS. SMS can be hijacked. Apps can't. If a platform offers hardware key support (Yubikey, for example), use that instead. It's overkill for most people, but it's the strongest option available.
Never use public WiFi for crypto transactions. Public WiFi is trivial to intercept. Your password, your seed phrase, your transaction confirmations, your private keys: all of it can be captured. This isn't theoretical. Do your crypto work on your home network or your mobile hotspot. That's it.
Assume every message claiming to be from a platform is fake until you verify it. Phishing emails, Discord DMs, Twitter replies: they're all designed to make you click a malicious link or enter your seed phrase. Legitimate platforms never ask for your seed phrase. Ever. If you got a message asking for it, report and block the sender. If you're unsure, go directly to the official website by typing the URL yourself. Don't click links in messages.
Keep your software updated. Your phone's operating system, your wallet software, your browser, your antivirus. Updates patch vulnerabilities. Staying on old versions is like leaving your front door unlocked while you advertise that nobody's home. This sounds basic because it is, but it's often skipped.
Consider using a separate device for crypto if you hold significant amounts. A dedicated phone or laptop that only handles wallet operations, signing transactions, and nothing else eliminates most malware vectors. This is extreme for most people. If you're holding $100,000 or more, it becomes reasonable.
What the OWASP Smart Contract Top 10 2026 tells us
In early 2026, the Open Web Application Security Project (OWASP) published the Smart Contract Top 10, ranking the most common smart contract vulnerabilities. The list includes reentrancy attacks (where a smart contract function calls another function that calls it back before the first execution completes), access control failures, and arithmetic issues. These aren't new problems. They're the problems that auditors look for.
Why mention this? Because when you see an audit from a firm that checks the OWASP Top 10 against the code, you know they're using a proven framework. It's not a guarantee, but it's a signal of professional work.
Your crypto holdings and insurance questions
One more thing: if you're holding crypto on an exchange for active trading, check whether that exchange has insurance. Major exchanges like Kraken and Coinbase offer some coverage. The limits are usually lower than you'd like, but it's better than zero. This is one reason to keep long-term holdings on a hardware wallet and active trading capital on an exchange. Different tools for different jobs.
FAQ
What's the safest way to store cryptocurrency?
Hardware wallets held in your personal possession, with your recovery seed written on paper and stored separately. This is non-custodial storage. You control the keys. Nobody can freeze your account, change the rules, or take your money without your permission. For amounts you hold long-term and don't trade frequently, this is the standard.
Are hardware wallets really necessary if I use a reputable exchange?
It depends on your holdings and risk tolerance. For small amounts you're actively trading, an exchange with insurance and strong security is fine. For amounts you're holding long-term, especially more than a few thousand dollars, a hardware wallet removes counterparty risk. The Bybit hack in 2025 hit users of a supposedly reputable exchange. Hardware wallets protect you from that scenario entirely.
How do I know if a DeFi protocol is safe to use?
Look for a recent audit from a recognized firm (CertiK, OpenZeppelin, Quantstamp, Trail of Bits). Read what the audit found and whether it was fixed. Check the protocol's history on DefiLlama's hacks tracker. Understand where the yield comes from. If the protocol is new and unaudited but offering massive returns, it's probably a scam. If it's been audited and used by other projects you trust, it's lower risk. No audit means no deposit of significant funds.
What should I do immediately if I think my wallet has been compromised?
First, don't panic. Move any remaining funds to a new wallet on a different device. Generate a new hardware wallet if you can. Check your transaction history to see what was stolen and when. If you were using an exchange account that's compromised, change the password and enable 2FA if you haven't already. Consider whether your email or other accounts were also breached (check haveibeenpwned.com). If you suspect a smart contract exploit rather than a personal hack, notify the protocol team immediately through official channels. Most exploits can't be reversed, but the team needs to know to fix the vulnerability.
Does using a VPN protect my crypto?
A VPN masks your IP address but doesn't protect your private keys or stop you from clicking malicious links. If you're worried about ISP surveillance or network-level attacks on public WiFi, a VPN helps. If you're worried about hacking, a VPN alone won't save you. Use a VPN for privacy. Use a hardware wallet and good habits for security. They're different problems with different solutions.
Securing your cryptocurrency in 2026 doesn't require becoming a security engineer. It requires discipline. Use a hardware wallet for long-term holdings. Enable 2FA. Check audit history before using DeFi. Verify every address before you send funds. Don't use public WiFi. Don't trust messages claiming to be from official sources until you verify them directly. These habits sound repetitive because they work. The crypto users who lose funds are almost never the ones following this checklist. They're the ones skipping it and assuming someone else did the work for them.
If DeFi is part of your strategy, go beyond basic security. Use platforms like Pistachio.fi that do the audit verification and protocol vetting for you. The yield isn't worth the risk if the protocol is compromised. Read through Pistachio's security overview or compare options on their best crypto yield platforms guide. The work upfront saves you from panic later.
Your cryptocurrency is as secure as your habits allow it to be. Make the habits good.
Published: March 3, 2026

Cross-chain crypto swaps: how Li.Fi powers Pistachio's one-tap zaps (2026)
Etherfuse stablebonds: earn government bond yields on-chain (2026)
How to earn money online in 2026 (crypto yield vs. the rest)

Linea crypto explained: what it is and how it works (2026)

Ethereum wallet guide 2026 (ethernet wallet explained)

DeFi Staking with Stader Labs: How ETHx Works in 2026

High-liquidity crypto exchanges: PancakeSwap guide 2026
What is Raydium? How Solana's AMM Works in 2026

Passive Income Ideas for 2026: 10 Ways That Actually Work
Hong Kong crypto news 2026: licenses, stablecoins, and regulation
©2026 Copyright, PistachioFi Inc.
©2026 Copyright, PistachioFi Inc.
©2026 Copyright, PistachioFi Inc.