Pistachio Security Overview
Pistachio Security Overview

Pistachio Security Overview
Pistachio Security Overview

Each part of our infrastructure from key management and smart account security to vault integration is designed to meet the highest standards of safety and composability.
Token Storage:
All sensitive tokens are stored using [SecureStore](https://docs.expo.dev/versions/latest/sdk/securestore/), leveraging OS-level encryption (Keychain for iOS, Keystore for Android) to protect credentials at rest.
User Authentication:
Authentication is secured through time-limited, single-use OTPs, preventing credential reuse and minimizing exposure to phishing or brute force attacks.
Funds & App Authentication Separation:
User funds are cryptographically protected independent of app-level authentication. This separation ensures that any compromise of app credentials or sessions does not affect access to assets, recovery mechanisms, or the security of private keys.
On-Device Key Management:
All cryptographic keys are generated or restored securely and stored on-device using native secure enclaves. These keys are never transmitted or exposed outside of the device environment.
Redundant Cloud-Backed Recovery with Liveliness Requirements:
Backup keys are encrypted and stored with Apple iCloud and Google Cloud services. These backups cannot be used in isolation:
Breaches from our company do not compromise funds.
Breaches of Apple or Google alone are insufficient due to liveliness checks enforced by Pistachio.
Breaches of the MPC layer (our third-party cryptographic key custody provider) cannot yield usable keys without simultaneously breaching both cloud providers and bypassing liveliness detection.
Each part of our infrastructure from key management and smart account security to vault integration is designed to meet the highest standards of safety and composability.
Token Storage:
All sensitive tokens are stored using [SecureStore](https://docs.expo.dev/versions/latest/sdk/securestore/), leveraging OS-level encryption (Keychain for iOS, Keystore for Android) to protect credentials at rest.
User Authentication:
Authentication is secured through time-limited, single-use OTPs, preventing credential reuse and minimizing exposure to phishing or brute force attacks.
Funds & App Authentication Separation:
User funds are cryptographically protected independent of app-level authentication. This separation ensures that any compromise of app credentials or sessions does not affect access to assets, recovery mechanisms, or the security of private keys.
On-Device Key Management:
All cryptographic keys are generated or restored securely and stored on-device using native secure enclaves. These keys are never transmitted or exposed outside of the device environment.
Redundant Cloud-Backed Recovery with Liveliness Requirements:
Backup keys are encrypted and stored with Apple iCloud and Google Cloud services. These backups cannot be used in isolation:
Breaches from our company do not compromise funds.
Breaches of Apple or Google alone are insufficient due to liveliness checks enforced by Pistachio.
Breaches of the MPC layer (our third-party cryptographic key custody provider) cannot yield usable keys without simultaneously breaching both cloud providers and bypassing liveliness detection.

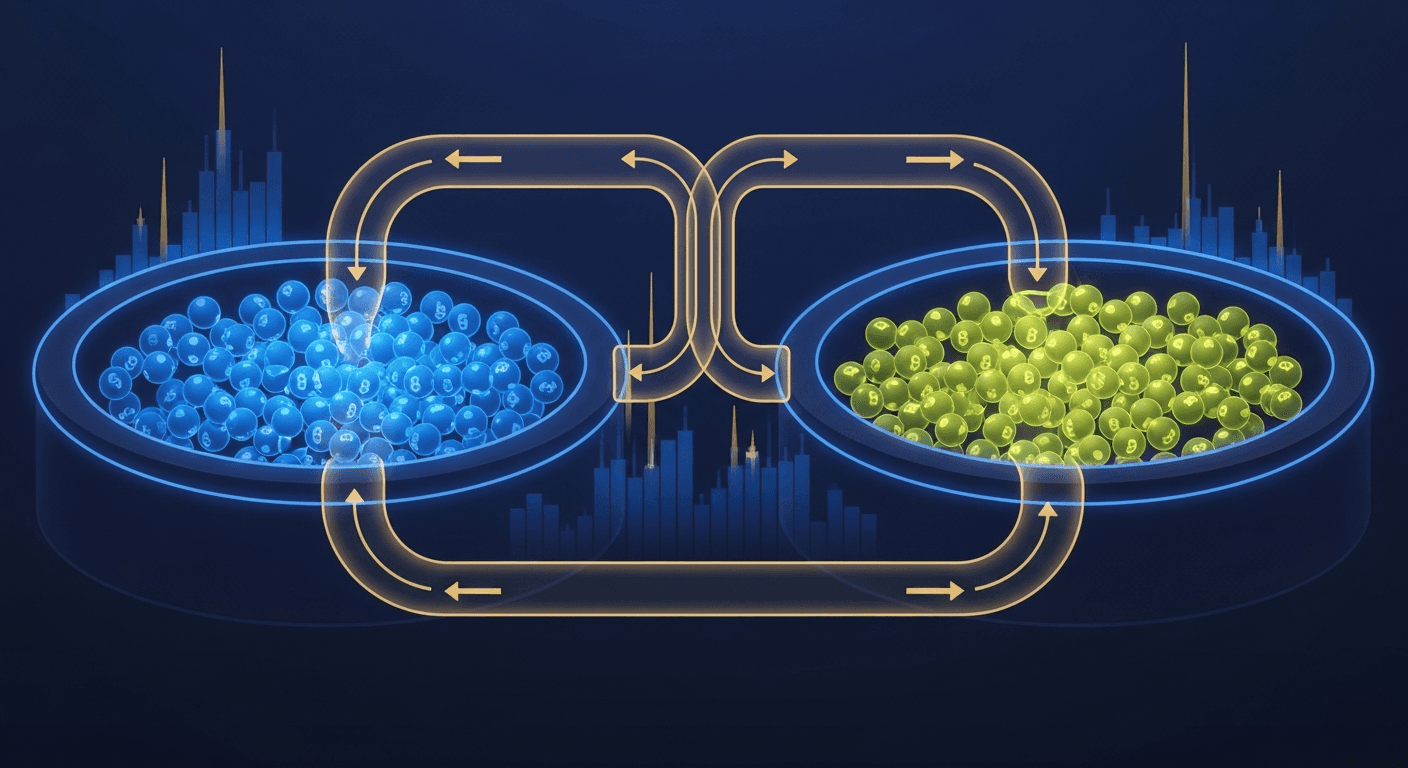
Cross-chain crypto swaps: how Li.Fi powers Pistachio's one-tap zaps (2026)
Etherfuse stablebonds: earn government bond yields on-chain (2026)
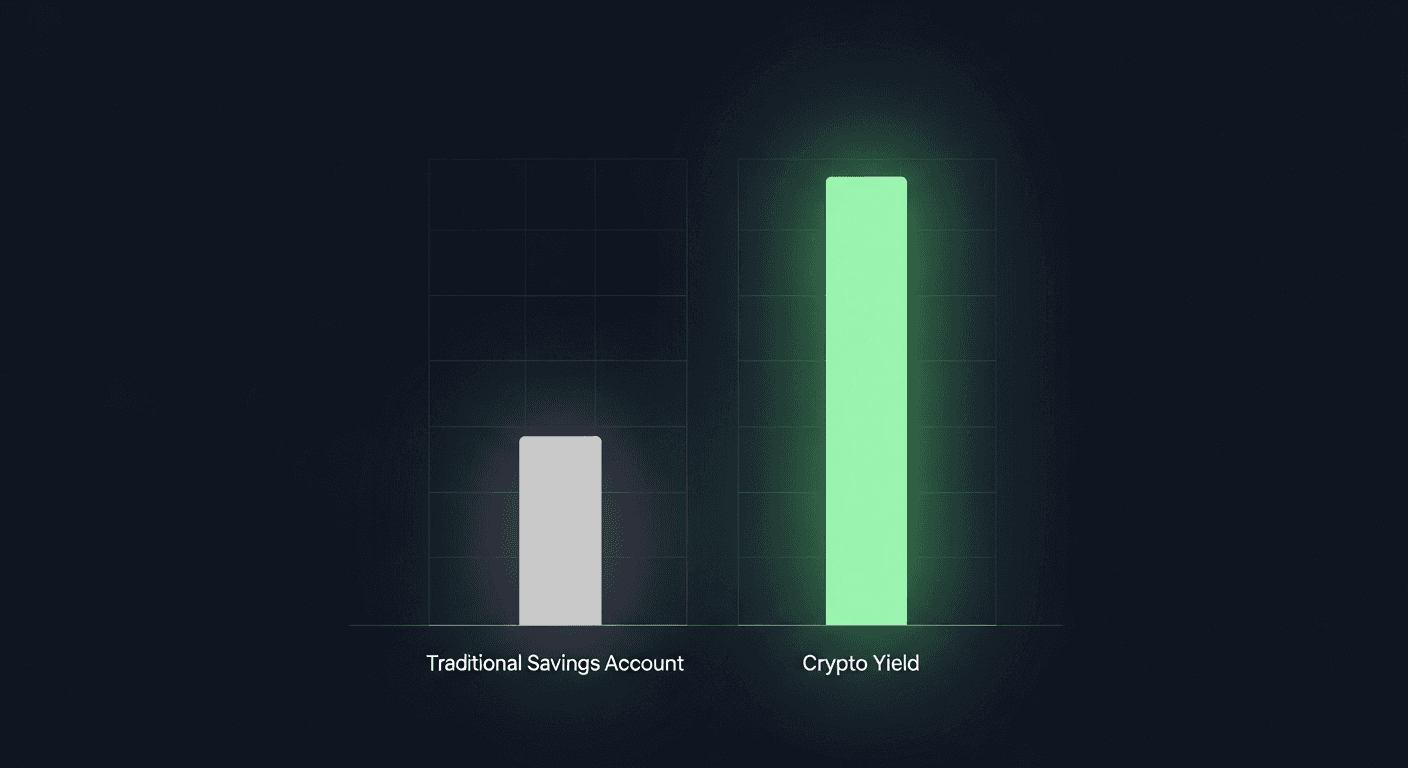
How to earn money online in 2026 (crypto yield vs. the rest)

Linea crypto explained: what it is and how it works (2026)

Ethereum wallet guide 2026 (ethernet wallet explained)

DeFi Staking with Stader Labs: How ETHx Works in 2026

High-liquidity crypto exchanges: PancakeSwap guide 2026
What is Raydium? How Solana's AMM Works in 2026

Passive Income Ideas for 2026: 10 Ways That Actually Work
Hong Kong crypto news 2026: licenses, stablecoins, and regulation
©2026 Copyright, PistachioFi Inc.
©2026 Copyright, PistachioFi Inc.
©2026 Copyright, PistachioFi Inc.